News & Updates
Product releases, integration announcements and industry insights from the EvTrack team.

New EvTrack Italian Distributor
EvTrack has appointed Gruppo Sirio in Modena, Italy, as its exclusive distributor for the Italian market. Gruppo Sirio provides access control and CCTV solution
Read more arrow_forward
EvTrack in Saudi Arabia - 24th ~ 28th Nov 2024
Successful road trip in Saudi Arabia during the month of November, demonstrating our visitor solution to the Saudi market.
Read more arrow_forward
EvTrack @ Intersec 2024 - Saudi Arabia
Just returned from Riyadh in the Kingdom of Saudi Arabia fresh from exhibiting at the Intersec Security Technology exhibition:What an incredible experience exhi
Read more arrow_forward
New EvTrack UAE Team Member
Very proud to welcome a new member to our United Arab Emirates 🇦🇪 team, Iftakhar Hasan who will be providing technical support and training to our EvTrack - Vis
Read more arrow_forward
Qatar Meetings
EvTrack - Visitor Management & Cloud Access Control is expanding its sales team and seeking a dynamic salesperson to cover the Pretoria, Midrand, and Johannesbu
Read more arrow_forward
The Grandfather of CCTV
EvTrack - Visitor Management & Cloud Access Control is expanding its sales team and seeking a dynamic salesperson to cover the Pretoria, Midrand, and Johannesbu
Read more arrow_forward
EvTrack is hiring - Johannesburg
EvTrack - Visitor Management & Cloud Access Control is expanding its sales team and seeking a dynamic salesperson to cover the Pretoria, Midrand, and Johannesbu
Read more arrow_forward
EvTrack will be at the Genetec Roadshow in Johannesburg 2024
April is going to be hectic ! Please visit us at the Genetec Roadshow in Joburg April 16th to see the Evtrack + SAFR from RealNetworks + Genetec’s Security Cent
Read more arrow_forward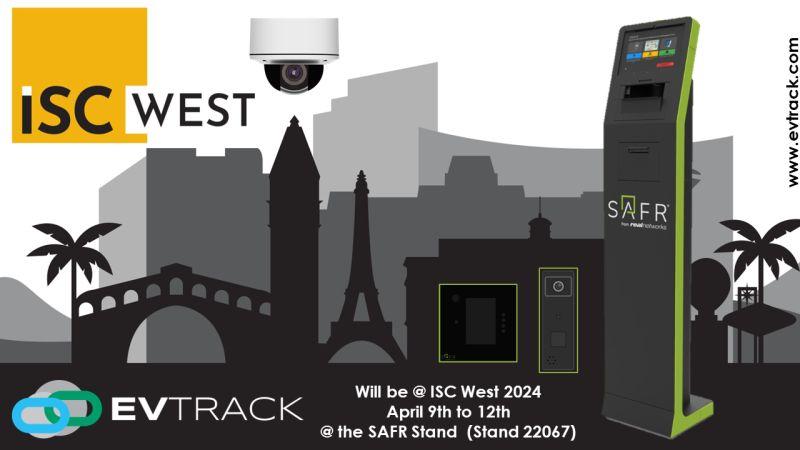
EvTrack will be at ISC West 2024 with SAFR
Visit EvTrack - Visitor Management & Cloud Access Control @ the Security Industry Association (SIA) ISC WEST Show in Las Vegas from the 9~12th April. Proudly ex
Read more arrow_forward
Vikas Vijayan Joins EvTrack In Charge of the UAE Region
EvTrack - Visitor Management & Cloud Access Control is excited to welcome its first Middle East region team member Vikas Vijayan. Vikas will be heading up our E
Read more arrow_forward
Suprema / Evtrack Integration at Intersec
Let EvTrack and ScreenCheck® Middle East help streamline your visitor to access control process with our Suprema Inc. Integration. Please visit stand SA-K11. We
Read more arrow_forward
Interesec
Please visit EvTrack - Visitor Management & Cloud Access Control & SAFR from RealNetworks at Intersec Middle East on the Aligntech International Stand S1-I11. L
Read more arrow_forward
Genetec Security Centre Saudi Arabia
EvTrack integrates with Genetec Security Centre for an integrated visitor-to-access control experience. Visitors can be registered using EvTrack's Handheld Devi
Read more arrow_forward
SC50 Mini Face Reader
Definitely the most exciting new product at the Intersec show in Saudi. The new SC50 mini face reader from SAFR from RealNetworks. This interview with Walter Ca
Read more arrow_forward
SIlo 3
EvTrack integrates with Genetec Security Centre for an integrated visitor-to-access control experience. Visitors can be registered using EvTrack's Handheld Devi
Read more arrow_forward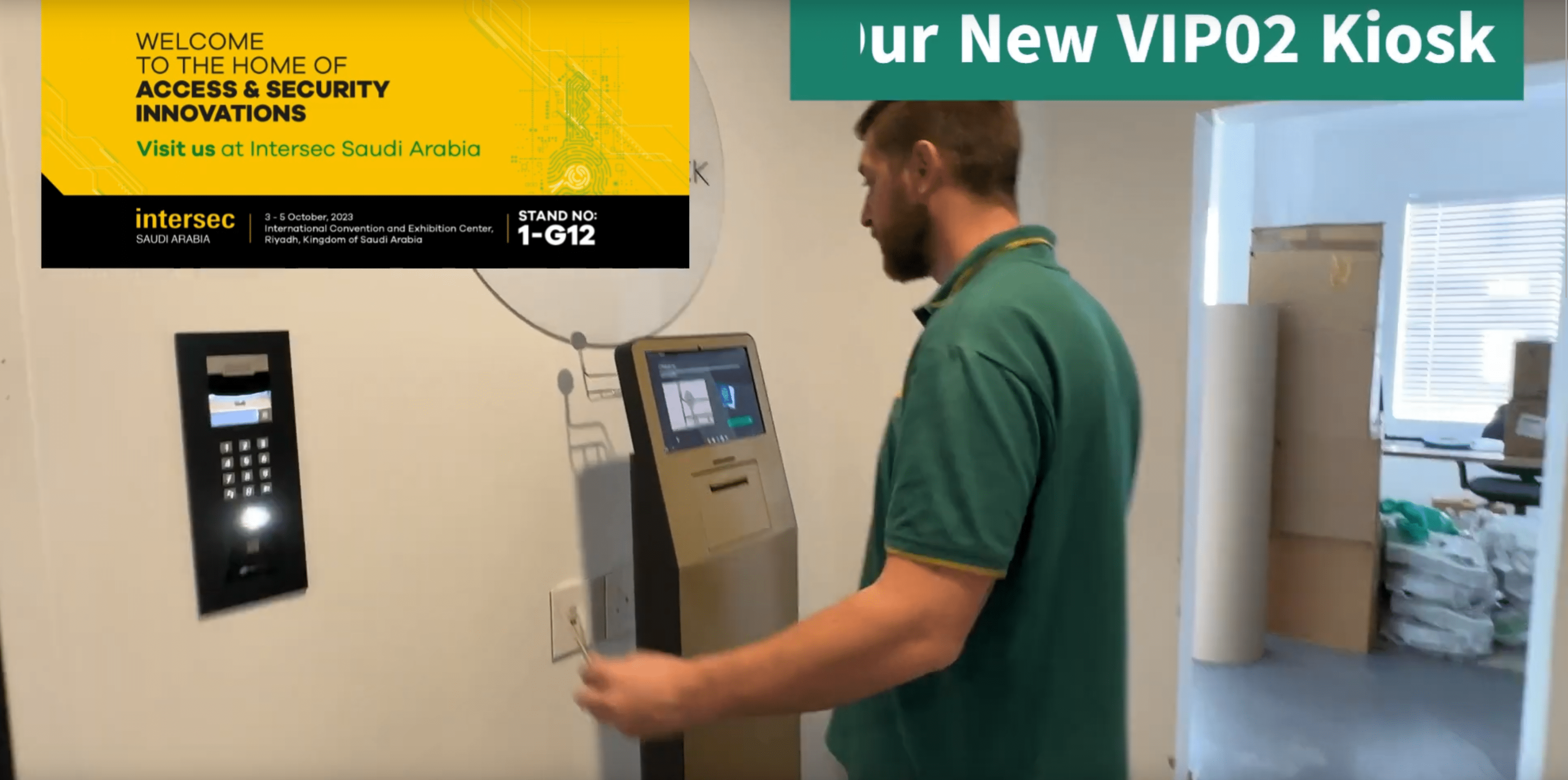
Intersec Saudi Arabia Visitor Kiosk to QR Code Access Control
Please visit EvTrack - Visitor Management & Cloud Access Control at Intersec Saudi Arabia in Riyadh. You can find us on the ScreenCheck Saudi Arabia stand 1-G12
Read more arrow_forward
Number Plate Recognition Cameras
Did you know EvTrack supports the Hanwha Vision range of ANPR / LPR IP cameras for visitor and employee vehicle access control. We support both the NumberOk and
Read more arrow_forward
Our 2N-compatible QR code reader
Our 2N-compatible QR code reader is ideal for visitor access control or applications needing contactless portable credentials without an app being required. Usi
Read more arrow_forward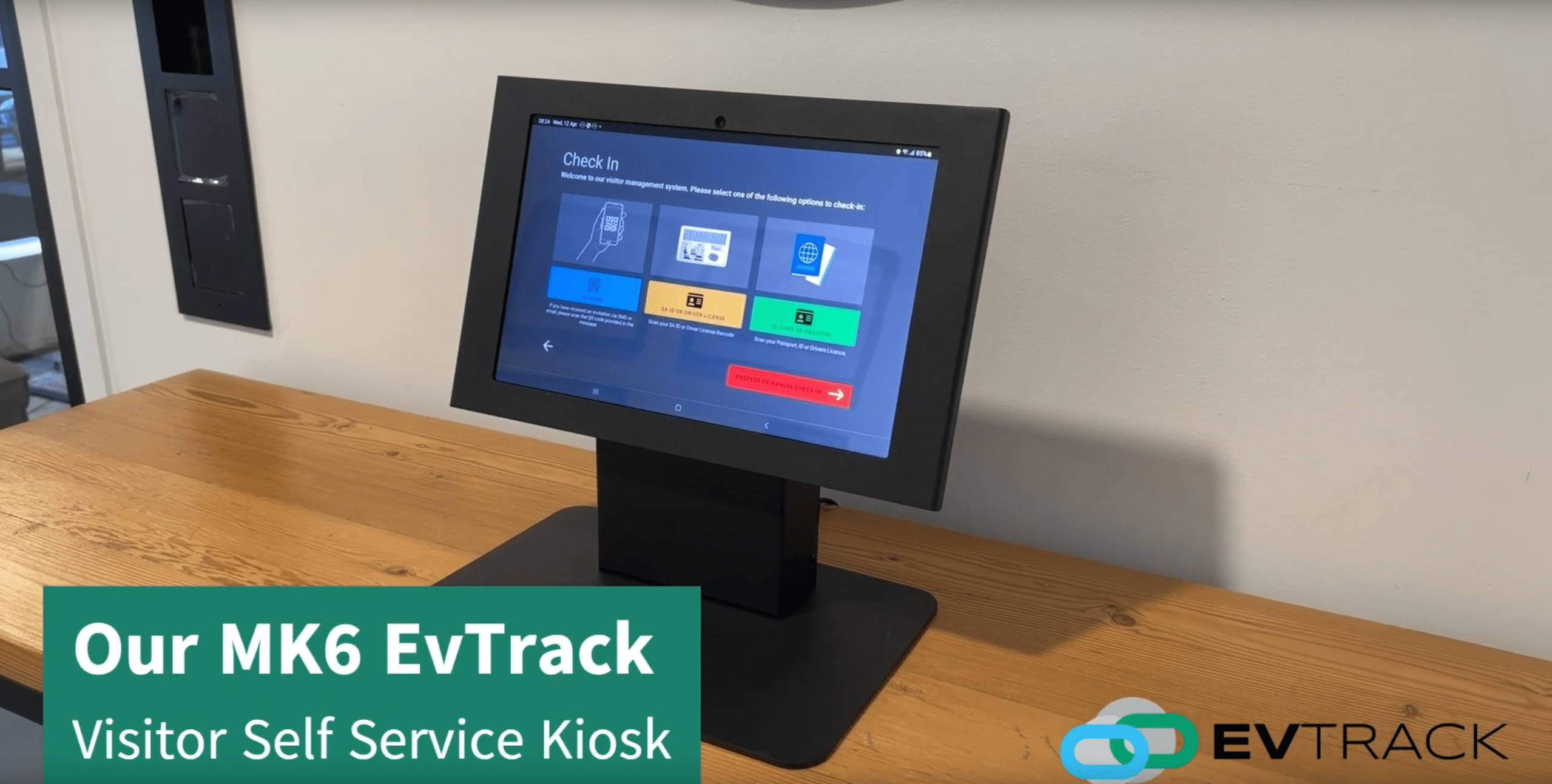
MK6 EvTrack visitor kiosk
Take a look at our MK6 EvTrack visitor kiosk. QR code scanning for pre-registered guests, ID + passport scanning & integration with 2N, SAFR from RealNetworks A
Read more arrow_forward
Supports Emirates ID Cards For Visitor Management
Looking for a super fast visitor management system that supports Emirates ID cards, we have you covered. EvTrack will be in Dubai 20~24th March. We interface wi
Read more arrow_forward
Happy New Year 2023
Wishing everyone Happy Festive Season & Happy New Year ! May 2022 only bring you all happiness and good health. From EvTrack - Visitor Management & Cloud Access
Read more arrow_forward
AirBnb Access Control Integration
Managing AirBnb guest access control can now be automated through EvTrack's integration with SuperSight's property management software for short term accommodat
Read more arrow_forward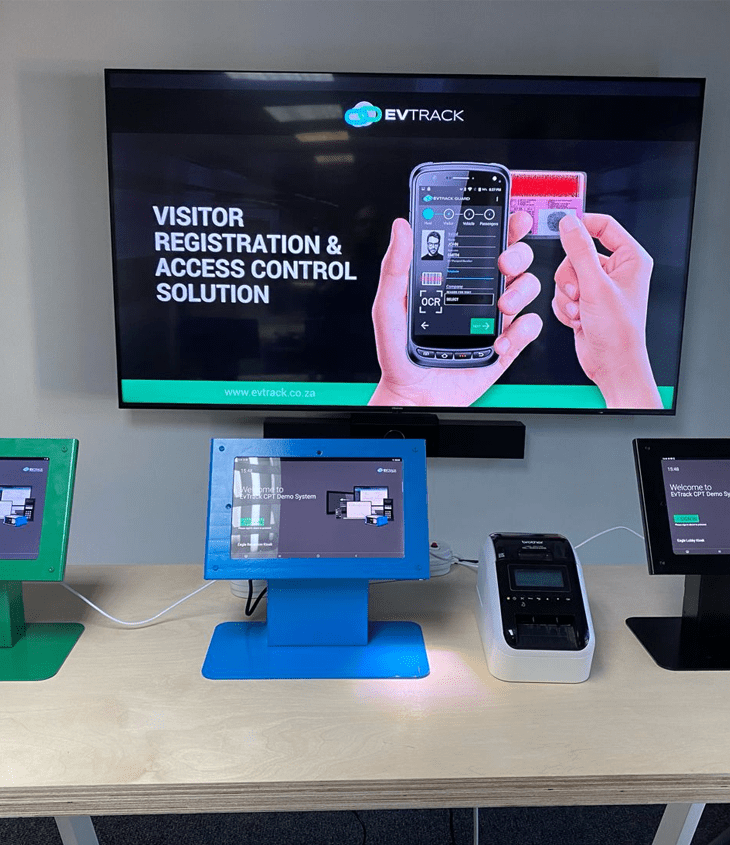
Convergint Technologies
We will be showcasing our new Evtrack FrontDesk Visitor Kiosk Solution at the Convergint Technologies Insight Summit this week Thursday 18th May. Don’t miss it!
Read more arrow_forward
QR Code Access Control
EvTrack - Visitor Management & Cloud Access Control is excited to be presenting at InSight Innovation Summit, hosted by Convergint Technologies on May 18th-20th
Read more arrow_forward
EVT-QR-2N-1 MOD 2N QR Code Reader
Very proud to be releasing our 2N TELEKOMUNIKACE a.s. compatible QR code reader for contactless access control. EvTrack - Visitor Management & Cloud Access Cont
Read more arrow_forward
Credential for Temporary Contactless Access Control
Still, the best Credential for Temporary Contactless Access Control did you know EvTrack - Visitor Management & Cloud Access Control has a full range of QR Code
Read more arrow_forward
Microsoft Visio Stencil
We have just released a set of free Access Control Visio shapes. Our stencil includes Axis, 2N and EvTrack shapes. With Tattile shapes to follow soon. Please do
Read more arrow_forward
EvTrack Access Control Technology Trends 2021
Now that we are in 2021 I thought we would share the access control trends we know will be important based on customer feedback & new projects. Really looking f
Read more arrow_forward
EvTrack Now in Saudi Arabia
To all my contacts in the Kingdom of Saudi Arabia. I am proud to announce that EvTrack - Visitor Management & Cloud Access Control is now available from Alsmari
Read more arrow_forward
Case Study 05: The Quarter – Cape Town South Africa
Case Study 05: The Quarter - Cape Town South Africa True Curb to Couch Access Control & Visitor Management Looking for True 'Curb to Couch' Access Control to g
Read more arrow_forward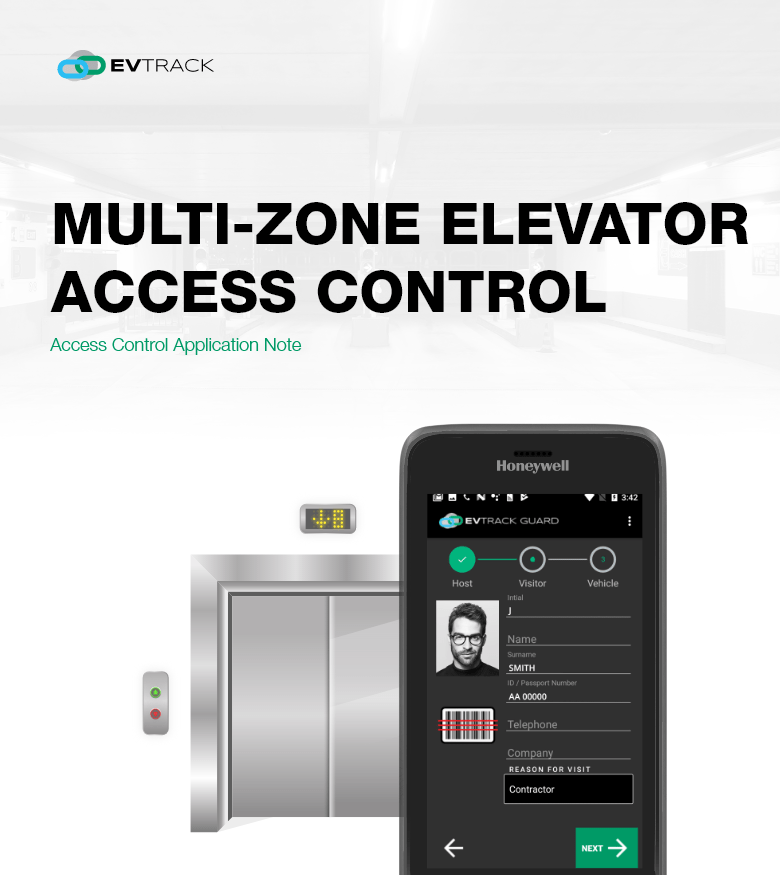
Multi-zone elevator access control
Multi-Zone Elevator Access Control Access Control Application Note The control of access into or out of elevators is important in order to protect residents and
Read more arrow_forward
10 Access Control Predictions For 2021
Access Control Predictions For 2021 2021 is set to be an interesting year for the access control industry with many new trends emerging. Here are some of our pr
Read more arrow_forward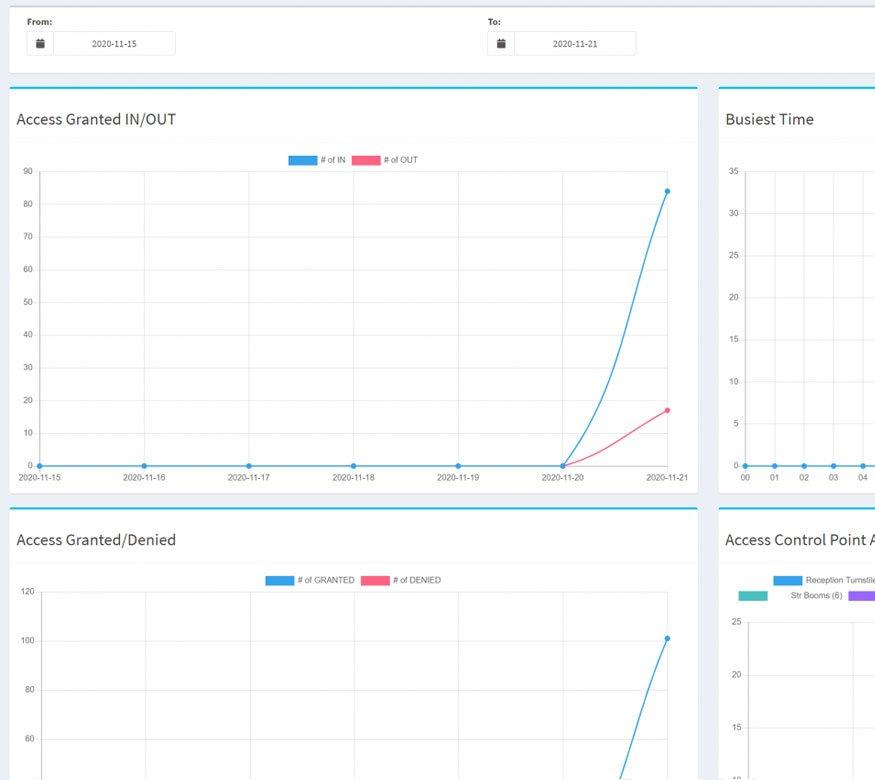
EvTrack Visitor Data Analytics
Blog Visitor Data Analytics November 21, 2020 Our data analytics feature analyses access control raw data to help security or building managers pick up access c
Read more arrow_forward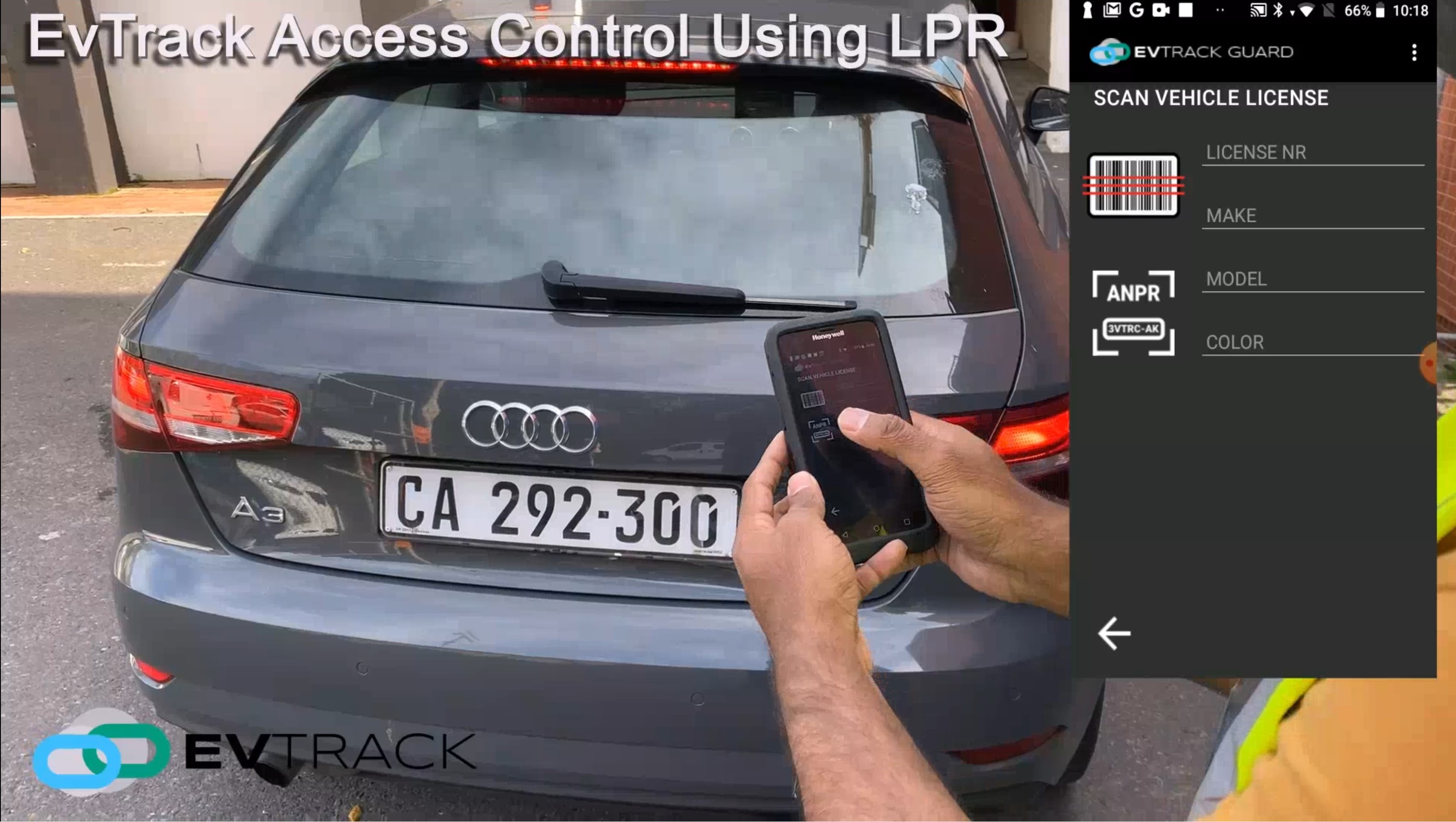
EvTrack Guard LPR Support
Blog EvTrack Guard LPR Support September 10, 2020 EvTrack Handheld License Plate Recognition Did you know EvTrack Guard now supports Automatic Numberplate Recog
Read more arrow_forward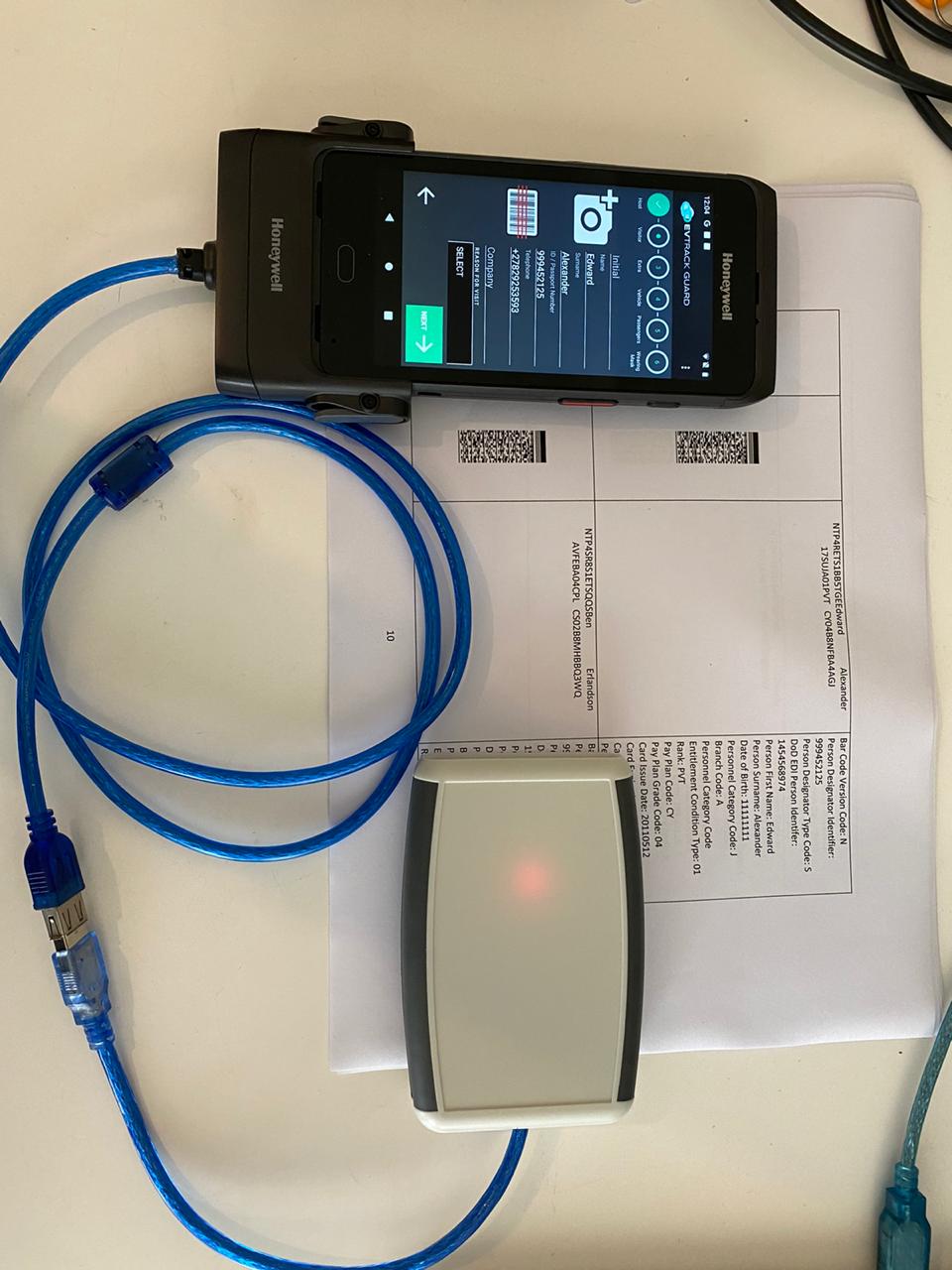
Common Access Card (CAC)
Blog Common Access Card (CAC) September 5, 2020 DoD Common Access Card (CAC) Barcode Support The Common Access Card (CAC) is an identification card used by the
Read more arrow_forward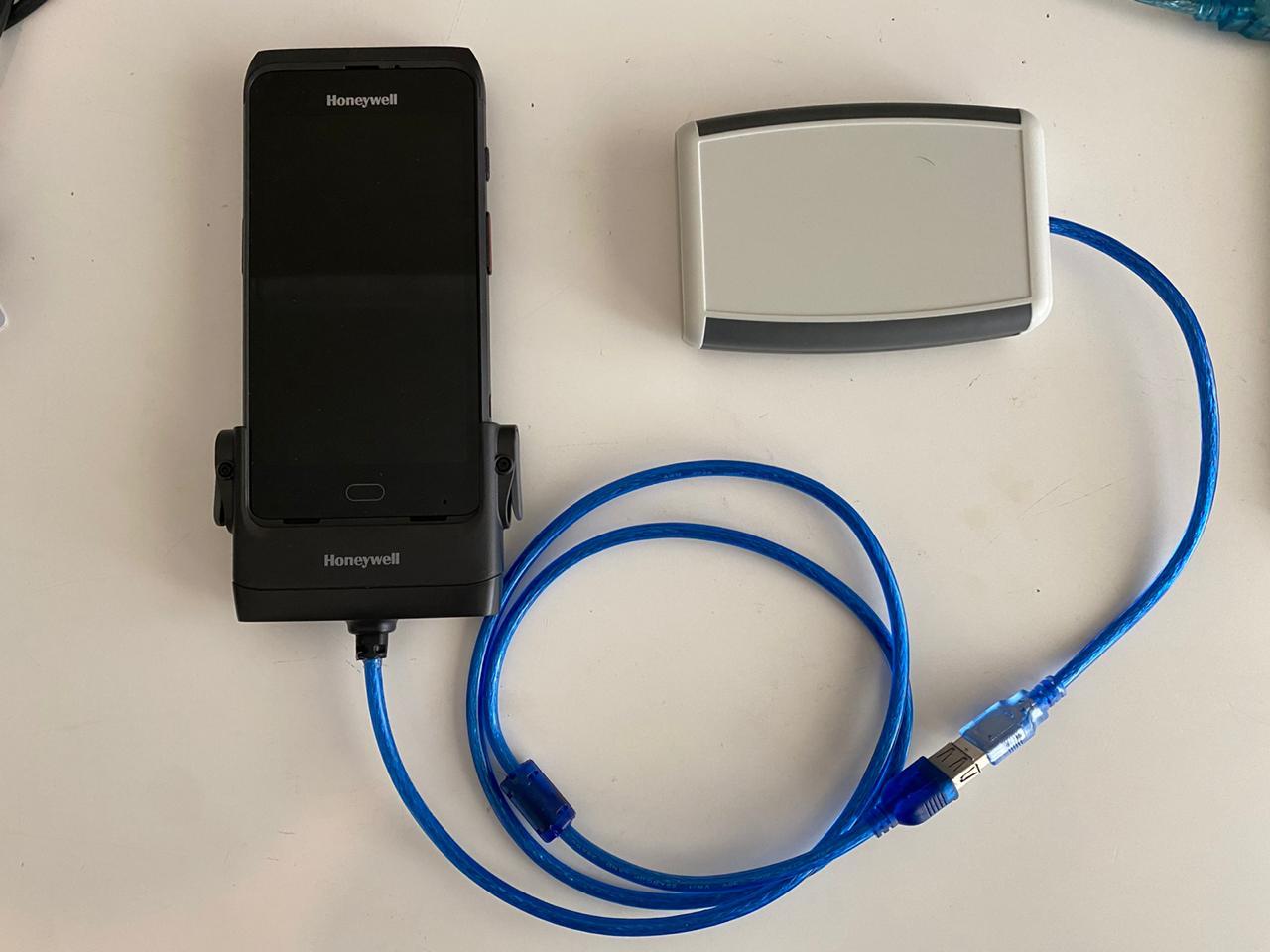
Honeywell CT40 Rugged Support
Blog Honeywell CT40 Rugged Support September 5, 2020 Honeywell CT40 Support The Honeywell CT40 is a rugged Android handheld computer for data capture applicatio
Read more arrow_forward
Sexy Turnstiles @ Intersec
Blog Sexy Turnstiles @ Intersec January 18, 2020
Read more arrow_forwardReady to Streamline Your Visitor Management?
Join hundreds of organisations worldwide using EvTrack for secure, seamless access control.

